A journal of my thoughts, adventures and experiences. #programming #software #photography #travel #leo
Tuesday, September 2, 2008
Well done beijing
I am proud to be an Asian!!
Thursday, July 31, 2008
Send Free SMS to Mobitel (Sri Lanka)
What you need to do is simply send a mail to phoneNumber@sms.mobitel.lk. For example, if you wanna send a SMS to 071-5373891 then simply send a mail to 94715373891@sms.mobitel.lk!
If you know PHP or ASP or Perl then you can use this concept to create a widget that can send SMS to user.
You can get phone number as an input and then if you can generate an email as I described above then you have created the widget. I have already created a widget to send free SMS using PHP. Here is the source code of that.
Client side
<html>
<head>
<title>root_j@hotmail.com</title>
</head>
<body>
<form method="POST" action="send.php">
<pp>
Number :-<input type="text" name="num" size="20"> Type online the Mobitel
number without 0 eg:- 714XXXXXX<br>
email:-<input type="text" name="email" size="20"><br>
Message<textarea rows="2" name="mess" cols="20"></textarea></p>
<p><input type="submit" value="Submit" name="B1"p>
<input type="reset" value="Reset" name="B2"></p>
</form>
</body>
</html>
server Side save it as send.php
<?php
$num=$_POST['num'];
$p_email=$_POST['email'];
$p_mess=$_POST['mess'];
$sendem = "94".$num."@sms.mobitel.lk";
$to = $sendem;
$subject = $p_email;
$message = $p_mess;
$from = $p_email;
$headers = "From: $from";
mail($to,$subject,$message,$headers);
echo "Message send!!";
echo "<br>";
?>
Recenly I heard that Dialog is also lanching such a service for MMS. You just want to send a mail to yournumber@mms.dialog.lk and receiver will get it as a MMS.
Unfortunately other operators such as Tigo, Hutch doesn’t offer such service!!! If you need to send them mail then you need to buy a SMS gateway, which is very expensive.
Tuesday, May 13, 2008
UoM Tops GSoc 2008
That's awesome! I'm proud to be an undergraduate of department of Computer Science of Engineering, Univ. of Moratuwa as CSE students started with one award 3 years ago and have bagged 18 GSoC awards this year. There is one ENTC student and another first year student
from the Faculty of Engineering. With a total of 24 awards for the entire
University.
Congratulations to all GSocers at University of Moratuwa !!
Keep Rocking !!!
Friday, April 25, 2008
SQL Server 2008 - The hierarchyid data type
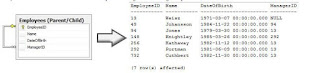 SQL Server 2008 introduces a new CLR data type called hierarchyid to make storing and querying hierarchical data much easier. Unlike the parent/child approach which focused on maintaining relationships among records, this approach stores data by keeping track of the hierarchical level of each record and its position within its given level. The data stored in a hierarchyid field looks similar to how directory structures in a file system are organized, except using numbers such like the sketch below.
SQL Server 2008 introduces a new CLR data type called hierarchyid to make storing and querying hierarchical data much easier. Unlike the parent/child approach which focused on maintaining relationships among records, this approach stores data by keeping track of the hierarchical level of each record and its position within its given level. The data stored in a hierarchyid field looks similar to how directory structures in a file system are organized, except using numbers such like the sketch below.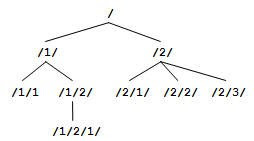 The entity instance at the helm of the hierarchy is recorded as the root (/). Subordinates of the root are recorded with their position numbers, such as /1/ for the first subordinate and /2/ for the second and so on. If by any chance
The entity instance at the helm of the hierarchy is recorded as the root (/). Subordinates of the root are recorded with their position numbers, such as /1/ for the first subordinate and /2/ for the second and so on. If by any chance- a subordinate is to be inserted between /1/ and /2/, it would be recorded as /1.1/ (since 1.1 naturally appears between 1 and 2, yet remember that this is not a decimal numbering system),
- and if a subordinate is to be inserted before /1/ it would be added as /0/,
- and to insert a subordinate in between /1/ and /1.1/ would result in the value /1.0/
But, all the above values are in the same level of the hierarchy (i.e. direct children of the root). Hierarchyid comes with several functions that you could use for various kinds of manipulations. It is also optimized to handle tree structures more efficiently, than the traditional parent/child approach.
Populating a column with hierarchyid values does not automatically relate the records of the table to each other, since there is no relationship defined between the records. It is up to the application to perform the placement of the records such that the hierarchy is properly formed. Take for instance the process of drawing an organizational chart for a business: The logical structure of the hierarchy is first drawn, then the employees are added to the sections of the hierarchy. Each section of the chart may not always be filled at once, since new employees may join the various ranks of the business at later times, neither is there a rule stating that the employees should be added to each section of the diagram in a particular order, such as a top-down method. Similarly the hierarchyid data type also possesses its own hierarchical structure defined within it. It is up to the application to pick the appropriate node, retrieve its value and then use it to insert into the table.
Getting down to business
Let us put the hierarchyid data type into use by creating a table of employees. The Employees table will be a simple one similar to the one used in Books Online:
1. Creating the table
CREATE TABLE [dbo].[Employees]
( [EmployeeID] hierarchyid NOT NULL, -- Primary Key of the HierarchyID data type
[EmployeeCode] char(4) NOT NULL, -- Business Key that uniquely identifies employees
[Name] varchar(20) NOT NULL, -- Name of the employee
[Title] varchar(20) NULL, -- Employee's title
PRIMARY KEY CLUSTERED ([EmployeeID] ASC),
CONSTRAINT unqEmployeeCode UNIQUE ([EmployeeCode])
)
GO
Note that the EmployeeID field has been set as the primary key and the EmployeeCode field has been assigned a unique constraint. The EmployeeCode is just a business key used to identify the entity.
2. Populating the Table
Let us start off the population by inserting the record of the top employee. This employee would be considered the root, hence let us add this record first (not that it requires to be done so). In situations where there is no single top employee, but three or four such people, we could forget about the root node, and go about adding nodes from the next level onwards. Let us take into account the following diagram which depicts our employees' organizational structure:
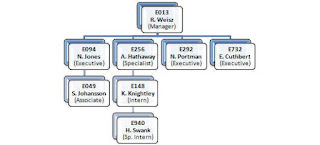 Since the root employee, let us start off by inserting employee E013's record:
Since the root employee, let us start off by inserting employee E013's record:INSERT INTO Employees (EmployeeID, EmployeeCode, Name, Title)
VALUES (hierarchyid::GetRoot(), 'E013', 'R. Weisz', 'Manager')
GO
We call the static GetRoot() function to return a hierarchyid value representing "root".
SELECT EmployeeID.ToString() AS 'EmployeeID_String', *
FROM Employees
GO
/* Results:
EmployeeID_String EmployeeID EmployeeCode Name Title
------------------ ---------- ------------- -------- -------
/ 0x E013 R. Weisz Manager
(1 row(s) affected)
*/
Since the hierarchyid value is not easily understandable, we need to cast it into a string by using the ToString() function. Note that it displays the value as "root" (/). Convert and Cast functions work as well.
Our next steps would be to insert the subordinate records. This process requires no specific order of insertion. Yet there are several options we need to look at before performing the inserts. Subordinates or child nodes can be placed (relative to the parent): 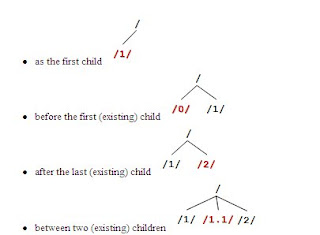
In order to add a child node we need to use the GetDescendant() method to generate a hierarchyid value from the specified parent node. The GetDescendant() method accepts two parameters: child1 and child2 which represent the two child nodes between which the new node is to be inserted. Therefore,
- if child1 and child2 are both NULL, no children exist; hence generate an id for a new child
- if child1 is NULL and child2 is NOT NULL, generate an id for a new child before child2
- if child1 is NOT NULL and child2 is NULL, generate an id for a new child after child1
- if child1 and child2 are both NOT NULL, generate an id for a new child between child1 and child2.
DECLARE @ParentID hierarchyid
SELECT @ParentID = hierarchyid::GetRoot()
INSERT INTO Employees (EmployeeID, EmployeeCode, Name, Title)
VALUES (@ParentID.GetDescendant(NULL, NULL), 'E292', 'N. Portman', 'Executive')
GO
/*
Results:
EmployeeID_String EmployeeCode Name Title
-------------------- ------------ ------------- -----------
/ E013 R. Weisz Manager
/1/ E292 N. Portman Executive
(2 row(s) affected)
*/
The @ParentID variable is used to obtain a reference to the parent node, which in this case is the root node. If the parent is not the root node, then the reference should be obtained from the appropriate record in the table. Similarly let us also add code to insert the rest of E013's children in the following sequence:
E094 as a child before an existing child node (before E292)
E732 as a child after an existing child node (after E292)
E256 as a child between two existing child nodes (between E292 and E732)
DECLARE @ParentID hierarchyid, @ChildID hierarchyid
SELECT @ParentID = hierarchyid::GetRoot() -- Retrieve Parent ID
SELECT @ChildID = EmployeeID FROM Employees
WHERE EmployeeCode = 'E292' -- Retrieve the only existing Child's ID
-- Insert Employee E094 before E292
INSERT INTO Employees (EmployeeID, EmployeeCode, Name, Title)VALUES (@ParentID.GetDescendant(NULL, @ChildID), 'E094', 'N. Jones', 'Executive')
/*
EmployeeID_String EmployeeID EmployeeCode Name Title
------------------- ------------ ------------ ------------ ----------
/ 0x E013 R. Weisz Manager
/0/ 0x48 E094 N. Jones Executive
/1/ 0x58 E292 N. Portman Executive
(3 row(s) affected)
*/
-- Insert Employee E732 after E292
INSERT INTO Employees (EmployeeID, EmployeeCode, Name, Title)
VALUES (@ParentID.GetDescendant(@ChildID, NULL), 'E732', 'E. Cuthbert', 'Executive')
/*
------------------- ------------ ------------ ------------ ----------
/ 0x E013 R. Weisz Manager
/0/ 0x48 E094 N. Jones Executive
/1/ 0x58 E292 N. Portman Executive
/2/ 0x68 E732 E. Cuthbert Executive
(4 row(s) affected)
*/
DECLARE @ChildID2 hierarchyidSELECT @ChildID2 = EmployeeID FROM Employees WHERE EmployeeCode = 'E732' -- Retrieve the ID of Employee E732
-- Insert Employee E256 between E292 and E732
INSERT INTO Employees (EmployeeID, EmployeeCode, Name, Title)VALUES (@ParentID.GetDescendant(@ChildID, @ChildID2), 'E256', 'A. Hathaway', 'Specialist')
/*
------------------- ------------ ------------ ------------ ----------
/ 0x E013 R. Weisz Manager
/0/ 0x48 E094 N. Jones Executive
/1/ 0x58 E292 N. Portman Executive
/1.1/ 0x62C0 E256 A. Hathaway Specialist
/2/ 0x68 E732 E. Cuthbert Executive
(5 row(s) affected)
*/
Similarly we could also add subordinates to the second level of employees that we just added. Much more simpler would be a stored procedure such as the one below:
CREATE PROC InsertEmployee
(
@ParentCode char(4),
@EmployeeCode char(4),
@Name varchar(20),
@Title varchar(20)
)
AS
BEGIN
DECLARE @ParentID hierarchyid, @ChildID1 hierarchyid, @ChildID2 hierarchyid, @ChildID hierarchyid
IF @ParentCode IS NOT NULL
SELECT @ParentID = EmployeeID FROM Employees WHERE EmployeeCode = @ParentCode
ELSE
SET @ParentID = hierarchyid::GetRoot()
SET TRANSACTION ISOLATION LEVEL SERIALIZABLE
BEGIN TRANSACTION
SELECT @ChildID2 = MIN(EmployeeID) FROM Employees
WHERE EmployeeCode > @EmployeeCode AND EmployeeID.GetAncestor(1) = @ParentID
SELECT @ChildID1 = MAX(EmployeeID) FROM Employees
WHERE EmployeeCode < @EmployeeCode AND EmployeeID.GetAncestor(1) = @ParentID
INERT INTO Employees (EmployeeID, EmployeeCode, Name, Title)
VALUES (@ParentID.GetDescendant(@ChildID1, @ChildID2), @EmployeeCode, @Name, @Title)
COMMIT TRANSACTION
END
GO
TRUNCATE TABLE InsertEmployee
EXEC InsertEmployee NULL, 'E013', 'R. Weisz', 'Manager'
EXEC InsertEmployee 'E013', 'E256', 'A. Hathaway', 'Specialist'
EXEC InsertEmployee 'E013', 'E094', 'N. Jones', 'Executive'
EXEC InsertEmployee 'E013', 'E792', 'E. Cuthbert', 'Executive'
EXEC InsertEmployee 'E013', 'E292', 'N. Portman', 'Executive'
EXEC InsertEmployee 'E094', 'E049', 'S. Johansson', 'Associate'
EXEC InsertEmployee 'E256', 'E148', 'K. Knightley', 'Intern'
EXEC InsertEmployee 'E148', 'E940', 'H. Swank', 'Special Intern'
The above stored procedure accepts the parent code to which the record has to be added under, the employee code, name and title of the new employee. This stored procedure however does not add a record for the root node, since it assumes that multiple employees could be at the top level of the employee hierarchy. It also adds the new employee in ascending order of the employee code.
Selecting Subordinates and Levels
The following two methods show how descendants of a particular node are retrieved.
DECLARE @CurEmployeeID hierarchyid
SELECT @CurEmployeeID = EmployeeID FROM Employees WHERE EmployeeCode = 'E256'
-- Code A
SELECT EmployeeID.ToString() AS 'EmployeeID_String', *
FROM Employees
WHERE @CurEmployeeID.IsDescendant(EmployeeID) = 1
/*
EmployeeID_String EmployeeCode Name Title
-------------------- ------------ -------------- ---------------
/1/1/ E256 A. Hathaway Specialist
/1/1/1/ E148 K. Knightley Intern
/1/1/1/1/ E940 H. Swank Special Intern
(3 row(s) affected)
*/
-- Code B
SELECT EmployeeID.ToString() AS 'EmployeeID_String', *
FROM Employees
WHERE EmployeeID.GetAncestor(1) = @CurEmployeeID
/*
EmployeeID_String EmployeeCode Name Title
-------------------- ------------ -------------- ---------------
/1/1/1/ E148 K. Knightley Intern
(1 row(s) affected)
*/
In the above code section, Code A uses the IsDescendant() function which returns true if the specified node is a descendant of the current node, hence the above code returns the sub-hierarchy of records. Code B makes use of the GetAncestor() function which gets the ancestor of the specified node at a given level. Therefore it returns the record of the node which has the current node as its ancestor at Level 1.
The following code uses the GetLevel() function to display the level of each node in the hierarchy.
SELECT EmployeeID.ToString() AS 'EmployeeID_String', EmployeeID.GetLevel() AS 'Level', *
/*
EmployeeID_String Level EmployeeID EmployeeCode Name Title
-------------------- ------ ------------ ------------ -------------- ---------------
/1/ 1 0x58 E013 R. Weisz Manager
/1/0/ 2 0x5A40 E094 N. Jones Executive
/1/0/1/ 3 0x5A56 E049 S. Johansson Associate
/1/1/ 2 0x5AC0 E256 A. Hathaway Specialist
/1/1/1/ 3 0x5AD6 E148 K. Knightley Intern
/1/1/1/1/ 4 0x5AD6B0 E940 H. Swank Special Intern
/1/1.1/ 2 0x5B16 E292 N. Portman Executive
/1/2/ 2 0x5B40 E792 E. Cuthbert Executive
(8 row(s) affected)
*/
Reordering Nodes
Then, there are situations when a record is required to be shifted under a new parent node. To perform this action we use the Reparent() function, which requires two parameters: the old parent hierarchyid and the new one. The following code shows how this can be done:
DECLARE @CurEmployeeID hierarchyid, @OldParentID hierarchyid, @NewParentID hierarchyid
SELECT @CurEmployeeID = EmployeeID
FROM Employees
WHERE EmployeeCode = 'E049'
SELECT @OldParentID = EmployeeID.GetAncestor(1) -- Retrieve the Current Parent ID
FROM Employees WHERE EmployeeID = @CurEmployeeID
SELECT @NewParentID = EmployeeID -- Retrieve the New (Target) Parent ID
FROM Employees WHERE EmployeeCode = 'E292'
UPDATE EmployeesSET EmployeeID = @CurEmployeeID.Reparent(@OldParentID, @NewParentID)WHERE EmployeeID = @CurEmployeeID
/*
EmployeeID_String EmployeeID EmployeeCode Name Title
-------------------- ------------- ------------ ------------- ---------------
/1/ 0x58 E013 R. Weisz Manager
/1/0/ 0x5A40 E094 N. Jones Executive
/1/1 0x5AC0 E256 A. Hathaway Specialist
/1/1/1/ 0x5AD6 E148 K. Knightley Intern
/1/1/1/1/ 0x5AD6B0 E940 H. Swank Special Intern
/1/1.1/ 0x5B16 E292 N. Portman Executive
/1/1.1/1/ 0x5B16B0 E049 S. Johansson Associate
/1/2/ 0x5B40 E792 E. Cuthbert Executive
(8 row(s) affected)
*/
Indexing HierarchyID
HierarchyID supports two types of indexing:
- Depth-first
- Breadth-first
The option of using either or both index types on your hierarchyid table depends on the types of queries and the frequency of running them.
A little more facts about hierarchyid
- Supposing that x and y are two hierarchyid values; x <>
- Arbitrary deletions are possible in a table with hierarchyid, but it could leave orphaned sub-trees. Hence, it is required that the application performs all required validations.
- Hierarchyid data types are extremely compact in size.
Though drawbacks such as the need for application based consistency maintenance is present, the hierarchyid data type provides improved querying over the parent/child and XML methods in many cases, and requires a little getting used to since it is a CLR data type. Code in this article was written and tested on SQL Server 2008 CTP - February 2008. Refer SQL Server 2008 Books Online for more information and tutorials.
Friday, April 11, 2008
Monday, April 7, 2008
Sri Lanka urges world to 'wake-up' on terror

The Minister died on the spot, along with 13 others including former Olympic marathoner K.A. Karunaratne and national athletics coach Lakshman de Alwis, in total more than 90 were wounded.
Friday, April 4, 2008
Dynamic Stored Procedures
http://www.4guysfromrolla.com/webtech/020600-1.shtml
If you would like the query plan, sp_executeSQL can be used for optimizations,
http://www.4guysfromrolla.com/webtech/sqlguru/q120899-2.shtml
2008 April Fools Jokes by popular web sites
> Google’s virgle projecthttp://www.google.com/virgle/index.html
> Google’s search the future beta (launched in google.au on 1st April http://www.google.com.au/intl/en/gday/index.html
> Microsoft and Yahoo agrees on buyout price (before this yahoo denied Microsoft’s offer to buy out yahoo)http://www.infoworld.com/article/08/04/01/14FE-april-fool-microsoft-yahoo_1.html
> Goal.com (England Replace Expelled Spain at Euro 2008)http://www.goal.com/en/Articolo.aspx?ContenutoId=642832
> freewebs.com (this redirects everything to a fake google.com and below you’ll see “2008® April Fools” http://aprilfoolsdayontheweb.com
> Scientists Harness Kinetic Energy from Keyboards (Best april fool’s day blog post)http://bobmccarty.com/2008/04/01/scientists-harness-kinetic-energy-from-keyboards/
Have FuN !! :-)
Dolls in a mans life :)
1........His Daughter, 'Baby doll'
2........His Girlfriend, 'Barbie doll'
3........His Wife, 'Panadol ' !! :-)
Thursday, April 3, 2008
Micro waved water - a MUST read
I am not sure how long he set the timer for, but he told me he wanted to bring the water to a boil.
When the timer shut the oven off, he removed the cup from the oven. As he looked into the cup, he noted that the water was not boiling, but instantly the water in the cup 'blew up' into his face. The cup remained intact until he threw it out of his hand but all the water had flown out into his face due to the build up of energy.
His whole face is blistered and he has 1st and 2nd degree burns to his face, which may leave scarring. He also may have lost partial sight in his left eye.
While at the hospital, the doctor who was attending to him stated that this is fairly common occurrence and water (alone) should never be heated in a microwave oven.. If water is heated in this manner, something should be placed in the cup to diffuse the energy such as: a wooden stir stick, tea bag, etc. It is however a much safer choice to boil the water in a tea kettle.
General Electric's (GE) response:
Thanks for contacting us. I will be happy to assist you.
The e-mail that you received is correct. Micro waved water and other liquids do not always bubble when they reach the boiling point. They can actually get superheated and not bubble at all.
The superheated liquid will bubble up out of the cup when it is moved or when something like a spoon or tea bag is put into it.
To prevent this from happening and causing injury,
Do not heat any liquid for more than two minutes per cup.
After heating, let the cup stand in the microwave for thirty seconds before moving it or adding anything into it.
Wednesday, April 2, 2008
Java Programming Style Guidelines
This document lists Java coding recommendations common in the Java development community.
http://geosoft.no/development/javastyle.html
The recommendations are based on established standards collected from a number of sources, individual experience, local requirements/needs, as well as suggestions
SQL Injection: What is it?
In essence, SQL Injection arises because the fields available for user input allow SQL statements to pass through and query the database directly.
SQL Injection: An In-depth Explanation
Web applications allow legitimate website visitors to submit and retrieve data to/from a database over the Internet using their preferred web browser. Databases are central to modern websites – they store data needed for websites to deliver specific content to visitors and render information to customers, suppliers, employees and a host of stakeholders. User credentials, financial and payment information, company statistics may all be resident within a database and accessed by legitimate users through off-the-shelf and custom web applications. Web applications and databases allow you to regularly run your business.
SQL Injection is the hacking technique which attempts to pass SQL commands (statements) through a web application for execution by the backend database. If not sanitized properly, web applications may result in SQL Injection attacks that allow hackers to view information from the database and/or even wipe it out.
Such features as login pages, support and product request forms, feedback forms, search pages, shopping carts and the general delivery of dynamic content, shape modern websites and provide businesses with the means necessary to communicate with prospects and customers. These website features are all examples of web applications which may be either purchased off-the-shelf or developed as bespoke programs.
These website features are all susceptible to SQL Injection attacks which arise because the fields available for user input allow SQL statements to pass through and query the database directly.
SQL Injection: A Simple Example
Take a simple login page where a legitimate user would enter his username and password combination to enter a secure area to view his personal details or upload his comments in a forum.
When the legitimate user submits his details, an SQL query is generated from these details and submitted to the database for verification. If valid, the user is allowed access. In other words, the web application that controls the login page will communicate with the database through a series of planned commands so as to verify the username and password combination. On verification, the legitimate user is granted appropriate access.
Through SQL Injection, the hacker may input specifically crafted SQL commands with the intent of bypassing the login form barrier and seeing what lies behind it. This is only possible if the inputs are not properly sanitised (i.e., made invulnerable) and sent directly with the SQL query to the database. SQL Injection vulnerabilities provide the means for a hacker to communicate directly to the database.
The technologies vulnerable to this attack are dynamic script languages including ASP, ASP.NET, PHP, JSP, and CGI. All an attacker needs to perform an SQL Injection hacking attack is a web browser, knowledge of SQL queries and creative guess work to important table and field names. The sheer simplicity of SQL Injection has fuelled its popularity.
Why is it possible to pass SQL queries directly to a database that is hidden behind a firewall and any other security mechanism?
Firewalls and similar intrusion detection mechanisms provide little or no defense against full-scale SQL Injection web attacks.
Since your website needs to be public, security mechanisms will allow public web traffic to communicate with your web application/s (generally over port 80/443). The web application has open access to the database in order to return (update) the requested (changed) information.
In SQL Injection, the hacker uses SQL queries and creativity to get to the database of sensitive corporate data through the web application.
SQL or Structured Query Language is the computer language that allows you to store, manipulate, and retrieve data stored in a relational database (or a collection of tables which organise and structure data). SQL is, in fact, the only way that a web application (and users) can interact with the database. Examples of relational databases include Oracle, Microsoft Access, MS SQL Server, MySQL, and Filemaker Pro, all of which use SQL as their basic building blocks.
SQL commands include SELECT, INSERT, DELETE and DROP TABLE. DROP TABLE is as ominous as it sounds and in fact will eliminate the table with a particular name.
In the legitimate scenario of the login page example above, the SQL commands planned for the web application may look like the following:
SELECT count(*)
FROM users_list_table
WHERE username=’FIELD_USERNAME’
AND password=’FIELD_PASSWORD”
In plain English, this SQL command (from the web application) instructs the database to match the username and password input by the legitimate user to the combination it has already stored.
Each type of web application is hard coded with specific SQL queries that it will execute when performing its legitimate functions and communicating with the database. If any input field of the web application is not properly sanitised, a hacker may inject additional SQL commands that broaden the range of SQL commands the web application will execute, thus going beyond the original intended design and function.
A hacker will thus have a clear channel of communication (or, in layman terms, a tunnel) to the database irrespective of all the intrusion detection systems and network security equipment installed before the physical database server.
Is my database at risk to SQL Injection?
SQL Injection is one of the most common application layer attacks currently being used on the Internet. Despite the fact that it is relatively easy to protect against SQL Injection, there are a large number of web applications that remain vulnerable.
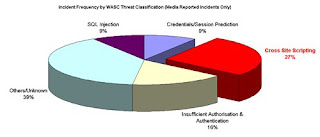
According to the Web Application Security Consortium (WASC) 9% of the total hacking incidents reported in the media until 27th July 2006 were due to SQL Injection. More recent data from our own research shows that about 50% of the websites we have scanned this year are susceptible to SQL Injection vulnerabilities.
It may be difficult to answer the question whether your web site and web applications are vulnerable to SQL Injection especially if you are not a programmer or you are not the person who has coded your web applications.
Our experience leads us to believe that there is a significant chance that your data is already at risk from SQL Injection.
Whether an attacker is able to see the data stored on the database or not, really depends on how your website is coded to display the results of the queries sent. What is certain is that the attacker will be able to execute arbitrary SQL Commands on the vulnerable system, either to compromise it or else to obtain information.
If improperly coded, then you run the risk of having your customer and company data compromised.
What an attacker gains access to also depends on the level of security set by the database. The database could be set to restrict to certain commands only. A read access normally is enabled for use by web application back ends.
Even if an attacker is not able to modify the system, he would still be able to read valuable information.
What is the impact of SQL Injection?
Once an attacker realizes that a system is vulnerable to SQL Injection, he is able to inject SQL Query / Commands through an input form field. This is equivalent to handing the attacker your database and allowing him to execute any SQL command including DROP TABLE to the database!
An attacker may execute arbitrary SQL statements on the vulnerable system. This may compromise the integrity of your database and/or expose sensitive information. Depending on the back-end database in use, SQL injection vulnerabilities lead to varying levels of data/system access for the attacker. It may be possible to manipulate existing queries, to UNION (used to select related information from two tables) arbitrary data, use subselects, or append additional queries.
In some cases, it may be possible to read in or write out to files, or to execute shell commands on the underlying operating system. Certain SQL Servers such as Microsoft SQL Server contain stored and extended procedures (database server functions). If an attacker can obtain access to these procedures, it could spell disaster.
Unfortunately the impact of SQL Injection is only uncovered when the theft is discovered. Data is being unwittingly stolen through various hack attacks all the time. The more expert of hackers rarely get caught.
Example of a SQLInjection Attack
Here is a sample basic HTML form with two inputs, login and password.
<form method="post" action="http://testasp.acunetix.com/login.asp"> <input name="tfUName" type="text" id="tfUName"> <input name="tfUPass" type="password" id="tfUPass"> </form>
The easiest way for the login.asp to work is by building a database query that looks like this:
SELECT id
FROM logins
WHERE username = '$username'
AND password = '$password’
If the variables $username and $password are requested directly from the user's input, this can easily be compromised. Suppose that we gave "Joe" as a username and that the following string was provided as a password: anything' OR 'x'='x
SELECT id
FROM logins
WHERE username = 'Joe'
AND password = 'anything' OR 'x'='x'
As the inputs of the web application are not properly sanitised, the use of the single quotes has turned the WHERE SQL command into a two-component clause.
The 'x'='x' part guarantees to be true regardless of what the first part contains.
This will allow the attacker to bypass the login form without actually knowing a valid username / password combination!
Cross site Scripting
Hackers are constantly experimenting with a wide repertoire of hacking techniques to compromise websites and web applications and make off with a treasure trove of sensitive data including credit card numbers, social security numbers and even medical records. Cross Site Scripting (also known as XSS or CSS) is generally believed to be one of the most common application layer hacking techniques.
 In general, cross-site scripting refers to that hacking technique that leverages vulnerabilities in the code of a web application to allow an attacker to send malicious content from an end-user and collect some type of data from the victim.
In general, cross-site scripting refers to that hacking technique that leverages vulnerabilities in the code of a web application to allow an attacker to send malicious content from an end-user and collect some type of data from the victim.Today, websites rely heavily on complex web applications to deliver different output or content to a wide variety of users according to set preferences and specific needs. This arms organizations with the ability to provide better value to their customers and prospects. However, dynamic websites suffer from serious vulnerabilities rendering organizations helpless and prone to cross site scripting attacks on their data.
"A web page contains both text and HTML markup that is generated by the server and interpreted by the client browser. Web sites that generate only static pages are able to have full control over how the browser interprets these pages. Web sites that generate dynamic pages do not have complete control over how their outputs are interpreted by the client. The heart of the issue is that if mistrusted content can be introduced into a dynamic page, neither the web site nor the client has enough information to recognize that this has happened and take protective actions." (CERT Coordination Center).
Cross Site Scripting allows an attacker to embed malicious JavaScript, VBScript, ActiveX, HTML, or Flash into a vulnerable dynamic page to fool the user, executing the script on his machine in order to gather data. The use of XSS might compromise private information, manipulate or steal cookies, create requests that can be mistaken for those of a valid user, or execute malicious code on the end-user systems. The data is usually formatted as a hyperlink containing malicious content and which is distributed over any possible means on the internet.
As a hacking tool, the attacker can formulate and distribute a custom-crafted CSS URL just by using a browser to test the dynamic website response. The attacker also needs to know some HTML, JavaScript and a dynamic language, to produce a URL which is not too suspicious-looking, in order to attack a XSS vulnerable website.
Any web page which passes parameters to a database can be vulnerable to this hacking technique. Usually these are present in Login forms, Forgot Password forms, etc…
N.B. Often people refer to Cross Site Scripting as CSS or XSS, which is can be confused with Cascading Style Sheets (CSS).Is your site vulnerable to Cross Site Scripting
Our experience leads us to conclude that the cross-site scripting vulnerability is one of the most highly widespread flaw on the Internet and will occur anywhere a web application uses input from a user in the output it generates without validating it. Our own research shows that over a third of the organizations applying for our free audit service are vulnerable to Cross Site Scripting. And the trend is upward.
Example of a Cross Site Scripting attack
As a simple example, imagine a search engine site which is open to an XSS attack. The query screen of the search engine is a simple single field form with a submit button. Whereas the results page, displays both the matched results and the text you are looking for.
Example:
Search Results for "XSS Vulnerability"
To be able to bookmark pages, search engines generally leave the entered variables in the URL address. In this case the URL would look like:
http://test.searchengine.com/search.php?q=XSS%20
Vulnerability
Next we try to send the following query to the search engine:
<script type="text/javascript"> alert('This is an XSS Vulnerability') </script>
By submitting the query to search.php, it is encoded and the resulting URL would be something like:
http://test.searchengine.com/search.php?q=%3Cscript%3
Ealert%28%91This%20is%20an%20XSS%20Vulnerability%92%2
9%3C%2Fscript%3E
Upon loading the results page, the test search engine would probably display no results for the search but it will display a JavaScript alert which was injected into the page by using the XSS vulnerability
How to check for Cross site scripting vulnerabilities
To check for Cross site scripting vulnerabilities, use a Web Vulnerability Scanner. A Web Vulnerability Scanner crawls your entire website and automatically checks for Cross Site Scripting vulnerabilities. It will indicate which URLs/scripts are vulnerable to these attacks so that you can fix the vulnerability easily. Besides Cross site scripting vulnerabilities a web application scanner will also check for SQL injection & other web vulnerabilities.
Preventing Cross Site Scripting attacks
To prevent these attacks, dangerous characters must be filtered out from the web application inputs. These should be filtered out both in their ASCII and HEX values.
Out of the 100,000 websites scanned by Acunetix WVS, 42% were found to be vulnerable to Cross Site Scripting. XSS is extremely dangerous and the number of the attacks is on the rise. Hackers are manipulating these vulnerabilities to steal organizations’ sensitive data. Can you afford to be next?
Cross Site Scripting allows an attacker to embed malicious JavaScript, VBScript, ActiveX, HTML, or Flash into a vulnerable dynamic page to fool the user, executing the script on his machine in order to gather data. Exploited Cross Site Scripting is commonly used to achieve the following malicious results:
Identity theft
Accessing sensitive or restricted information
Gaining free access to otherwise paid for content
Spying on user’s web browsing habits
Altering browser functionality
Public defamation of an individual or corporation
Web application defacement
Denial of Service attacks
Scan your website for Cross Site Scripting Vulnerabilities at no cost
Acunetix WVS Free Edition will scan your website for Cross Site Scripting vulnerabilities and it will also reveal the essential information related to it: such as the location of the vulnerability and techniques to fix the problem.
Tuesday, March 18, 2008
Mobile Phone Testing Platform on Internet
DeviceAnywhere is a revolutionary online service of MobileComplete that provides access to hundreds of real handsets, on live worldwide networks, remotely over the Internet - for all your dev/porting/testing needs.
Read more at
http://www.wired.com/gadgets/wireless/news/2007/10/iphone_dev_platform
Tri Lingual Email
It's COOL !!
http://www.esrilanka.lk/esrilanka/src/login.php
Tuesday, March 11, 2008
Good Read on TCP/IP
Read this!!
http://www.newartisans.com/blog_files/life.and.times.tcp.packet.php#unique-entry-id-42
Global Incidents Map
http://www.globalincidentmap.com/home.php
Click on any icon on the map for text update information. It's not just about Terrorism - it's about everything happening every minute some place in the world of terrorism threats, explosions, airline incidents, etc.
Monday, March 3, 2008
SQL Trigger Order Control
I have two triggers defined on my table which are set to fire on the same table actions (i.e. an INSERT, DELETE, UPDATE transaction). The second trigger that fires is dependent on the first fired trigger. How can I make sure that they fire in the correct order to enforce my business logic? In addition, as our system changes, what are some of the caveats that I need to be aware of when managing the trigger firing order?
http://www.mssqltips.com/tip.asp?tip=1409
Now I'm going to love .NET
http://weblogs.asp.net/scottgu/archive/2008/01/16/net-framework-library-source-code-now-available.aspx
Friday, February 29, 2008
Defend Your ASP.NET Web Sites against Evil Bots
While this might sound like a sci-fi promotion for the next Terminator or Transformers movie, in a way, that ominous sci-fi future is already here. But don’t be too afraid — just like in the movies, there are robots here to help us, too.
Find more about Defending Your ASP.NET Web Sites against Evil Bots at
http://steveorr.net/articles/CAPTCHASP.aspx
Thursday, February 28, 2008
How to use java script with ASP.NET 2.0
More info can be found at;
http://dotnetslackers.com/articles/aspnet/JavaScript_with_ASP_NET_2_0_Pages_Part1.aspx
Unlocker
Ever had such an annoying message given by Windows?
It has many other flavors:
>> Cannot delete file:
>> Access is deniedThere has been a sharing violation.
>> The source or destination file may be in use.
>> The file is in use by another program or user.
>> Make sure the disk is not full or write-protected and that the file is not currently in use.
Unlocker is the solution!
For more information refer the following URL. http://ccollomb.free.fr/unlocker/
Top 10 Largest Databases in the World
We all collected things as children. Rocks, baseball cards, Barbies, perhaps even bugs -- we all tried to gather up as much stuff as possible to compile the biggest most interesting collection possible. Some of you may have even been able to amass a collection of items numbering into the hundreds (or thousands).
As the story always goes, we got older, our collections got smaller, and eventually our interests died out...until now.
There are currently organizations around the world in the business of amassing collections of things, and their collections number into and above the trillions. In many cases these collections, or databases, consist of items we use every day.
In this list, we cover the top 10 largest databases in the world:
10. Library of Congress
Not even the digital age can prevent the world's largest library from ending up on this list. The Library of Congress (LC) boasts more than 130 million items ranging from cook books to colonial newspapers to U.S. government proceedings. It is estimated that the text portion of the Library of Congress would comprise 20 terabytes of data. The LC expands at a rate of 10,000 items per day and takes up close to 530 miles of shelf space -- talk about a lengthy search for a book.
If you're researching a topic and cannot find the right information on the internet, the Library of Congress should be your destination of choice. For users researching U.S. history, around 5 million pieces from the LC's collection can be found online at American Memory.
Unfortunately for us, the Library of Congress has no plans of digitizing the entirety of its contents and limits the people who can check out materials to Supreme Court Justices, members of Congress, their respective staff, and a select few other government officials; however, anyone with a valid Reader Identification Card (the LC's library card) can access the collection.
By the Numbers
130 million items (books, photographs, maps, etc)
29 million books
10,000 new items added each day
530 miles of shelves
5 million digital documents
20 terabytes of text data
9. Central Intelligence Agency
The Central Intelligence Agency (CIA) is in the business of collecting and distributing information on people, places and things, so it should come as no surprise that they end up on this list. Although little is known about the overall size of the CIA's database, it is certain that the agency has amassed a great deal of information on both the public and private sectors via field work and digital intrusions.
Portions of the CIA database available to the public include the Freedom of Information Act (FOIA) Electronic Reading Room, The World Fact Book, and various other intelligence related publications. The FOIA library includes hundreds of thousands of official (and occasionally ultra-sensitive) U.S. government documents made available to the public electronically. The library grows at a rate of 100 articles per month and contains topics ranging from nuclear development in Pakistan to the type of beer available during the Korean War. The World Fact Book boasts general information on every country and territory in the world including maps, population numbers, military capabilities and more.
By the Numbers
100 FOIA items added each month
Comprehensive statistics on more than 250 countries and entities
Unknown number of classified information
8. Amazon
Amazon, the world's biggest retail store, maintains extensive records on its 59 million active customers including general personal information (phone number address, etc), receipts, wishlists, and virtually any sort of data the website can extract from its users while they are logged on. Amazon also keeps more than 250,000 full text books available online and allows users to comment and interact on virtually every page of the website, making Amazon one of the world's largest online communities.
This data coupled with millions of items in inventory Amazon sells each year -- and the millions of items in inventory Amazon associates sell -- makes for one very large database. Amazon's two largest databases combine for more than 42 terabytes of data, and that's only the beginning of things. If Amazon published the total number of databases they maintain and volume of data each database contained, the amount of data we know Amazon houses would increase substantially.
But still, you say 42 terabytes, that doesn't sound like so much. In relative terms, 42 terabytes of data would convert to 37 trillion forum posts.
By the Numbers
59 million active customers
More than 42 terabytes of data
7. YouTube
After less than two years of operation YouTube has amassed the largest video library (and subsequently one of the largest databases) in the world. YouTube currently boasts a user base that watches more than 100 million clips per day accounting for more than 60% of all videos watched online.
In August of 2006, the Wall Street Journal projected YouTube's database to the sound of 45 terabytes of videos. While that figure doesn't sound terribly high relative to the amount of data available on the internet, YouTube has been experiencing a period of substantial growth (more than 65,000 new videos per day) since that figures publication, meaning that YouTube's database size has potentially more than doubled in the last 5 months.
Estimating the size of YouTube's database is particularly difficult due to the varying sizes and lengths of each video. However if one were truly ambitious (and a bit forgiving) we could project that the YouTube database will expect to grow as much as 20 terabytes of data in the next month.
Given: 65,000 videos per day X 30 days per month = 1,950,000 videos per month; 1 terabyte = 1,048,576 megabytes. If we assume that each video has a size of 1MB, YouTube would expect to grow 1.86 terabytes next month. Similarly, if we assume that each video has a size of 10MB, YouTube would expect to grow 18.6 terabytes next month.
By the Numbers
100 million videos watched per day
65,000 videos added each day
60% of all videos watched online
At least 45 terabytes of videos
6. ChoicePoint
Imagine having to search through a phone book containing a billion pages for a phone number. When the employees at ChoicePoint want to know something about you, they have to do just that. If printed out, the ChoicePoint database would extend to the moon and back 77 times.
ChoicePoint is in the business of acquiring information about the American population -- addresses and phone numbers, driving records, criminal histories, etc., ChoicePoint has it all. For the most part, the data found in ChoicePoint's database is sold to the highest bidders, including the American government.
But how much does ChoicePoint really know? In 2002 ChoicePoint was able to help authorities solve a serial rapist case in Philadelphia and Fort Collins after producing a list of 6 potential suspects by data mining their DNA and personal records databases. In 2001 ChoicePoint was able to identify the remains of World Trade Center victims by matching DNA found in bone fragments to the information provided by victim's family members in conjunction to data found in their databases.
By the Numbers
250 terabytes of personal data
Information on 250 million people
5. Sprint
Sprint is one of the world's largest telecommunication companies as it offers mobile services to more than 53 million subscribers, and prior to being sold in May of 2006, offered local and long distance land line packages.
Large telecommunication companies like Sprint are notorious for having immense databases to keep track of all of the calls taking place on their network. Sprint's database processes more than 365 million call detail records and operational measurements per day. The Sprint database is spread across 2.85 trillion database rows making it the database with the largest number of rows (data insertions if you will) in the world. At its peak, the database is subjected to more than 70,000 call detail record insertions per second.
By the Numbers
2.85 trillion database rows.
365 million call detail records processed per day
At peak, 70,000 call detail record insertions per second
4. Google
Although there is not much known about the true size of Google's database (Google keeps their information locked away in a vault that would put Fort Knox to shame), there is much known about the amount of and types of information Google collects.
On average, Google is subjected to 91 million searches per day, which accounts for close to 50% of all internet search activity. Google stores each and every search a user makes into its databases. After a years worth of searches, this figure amounts to more than 33 trillion database entries. Depending on the type of architecture of Google's databases, this figure could comprise hundreds of terabytes of information.
Google is also in the business of collecting information on its users. Google combines the queries users search for with information provided by the Google cookies stored on a user's computer to create virtual profiles.
To top it off, Google is currently experiencing record expansion rates by assimilating into various realms of the internet including digital media (Google Video, YouTube), advertising (Google Ads), email (GMail), and more. Essentially, the more Google expands, the more information their databases will be subjected to.
In terms of internet databases, Google is king.
By the Numbers
91 million searches per day
accounts for 50% of all internet searches
Virtual profiles of countless number of users
3. AT&T
Similar to Sprint, the United States' oldest telecommunications company AT&T maintains one of the world's largest databases. Architecturally speaking, the largest AT&T database is the cream of the crop as it boasts titles including the largest volume of data in one unique database (312 terabytes) and the second largest number of rows in a unique database (1.9 trillion), which comprises AT&T's extensive calling records.
The 1.9 trillion calling records include data on the number called, the time and duration of the call and various other billing categories. AT&T is so meticulous with their records that they've maintained calling data from decades ago -- long before the technology to store hundreds of terabytes of data ever became available. Chances are, if you're reading this have made a call via AT&T, the company still has all of your call's information.
By the Numbers
323 terabytes of information
1.9 trillion phone call records
2. National Energy Research Scientific Computing Center
The second largest database in the world belongs to the National Energy Research Scientific Computing Center (NERSC) in Oakland, California. NERSC is owned and operated by the Lawrence Berkeley National Laboratory and the U.S. Department of Energy. The database is privy to a host of information including atomic enegry research, high energy physics experiements, simulations of the early universe and more. Perhaps our best bet at traveling back in time is to fire up NERSC's supercomputers and observe the big bang.
The NERSC database encompasses 2.8 petabytes of information and is operated by more than 2,000 computational scientists. To put the size of NERSC into perspective, the total amount of spoken words in the history of humanity is estimated to be at 5 exabytes; in relative terms, the NERSC database is equivalent to 0.055% of the size of that figure.
Although that may not seem a lot at first glance, when you factor in that 6 billion humans around the globe speak more than 2,000 words a day, the sheer magnitude of that number becomes apparent.
By the Numbers
2.8 petabytes of data
Operated by 2,000 computational scientists
1. World Data Centre for Climate
If you had a 35 million euro super computer lying around what would you use it for? The stock market? Building your own internet? Try extensive climate research -- if there's a machine out there that has the answer for global warming, this one might be it. Operated by the Max Planck Institute for Meteorology and German Climate Computing Centre, The World Data Centre for Climate (WDCC) is the largest database in the world.
The WDCC boasts 220 terabytes of data readily accessible on the web including information on climate research and anticipated climatic trends, as well as 110 terabytes (or 24,500 DVD's) worth of climate simulation data. To top it off, six petabytes worth of additional information are stored on magnetic tapes for easy access. How much data is six petabyte you ask? Try 3 times the amount of ALL the U.S. academic research libraries contents combined.
By the Numbers
220 terabytes of web data
6 petabytes of additional data
* Additional Databases
The following databases were unique (and massive) in their own right, and just fell short of the cut on our top 10 list.
Nielsen Media Research / Nielsen Net Ratings
Best known for its television audience size and composition rating abilities, the U.S. firm Nielsen Media Research is in the business of measuring mass-media audiences including television, radio, print media, and the internet. The database required to process such statistics as Google's daily internet searches is nothing short of massive.
Myspace
It would seem appropriate that the world's largest social networking site, Myspace, has a rather large database to keep up with all of its user's content.
United States Customs
The U.S. Customs database is unique in that it requires information on hundreds of thousands of people and objects entering and leaving the United States borders instantaneously. For this to be possible, the database was special programmed to process queries near instantaneously.
HPSS
There are various databases around the world using technology similar to that found in our countdown's second largest database NERSC. The technology is known as High Performance Storage System or HPSS. Several other massive HPSS databases include Lawrence Livermore National Laboratory, Sandia National Laboratories, Los Alamos National Laboratory, Commissariat a l'Energie Atomique Direction des Applications Militaires, and more.


